Security Session „SQL Attack..ed“
– Attack scenarios on SQL Server (“Hacking SQL Server”)
At this year’s SQLSaturday in Germany I have shown one of my sessions again, in which I concentrate on “attack”. For me a great opportunity to dive deep into SQL Server Security and several penetration-test-tool, and to explore SQL Server for pitfalls and security configuration. At the end I had a long list of possible demonstrations. Among them a just recently developed DoS-attack via SQL Injection (at least I did not find any cue on a description for this kind of attack anywhere or got an answer on my inquiries), as well as a “privilege elevation”, which in this form seems to be quite unknown as well. – Everything is just done by exploiting customized settings and not by weaknesses in the engine (!).
Since there are barely any nameable sessions on this topic specifically for SQL Server in Germany (even at the Summits in the US I tended to be quite alone with my sessions on security), and I enjoy this topic in this a lot, I have decided to collect all possible topics here. I will not only present them on upcoming conferences in Europe or the US, but also I am offering these to the regional chapter leaders in Germany – “help yourself” – style 🙂
An einem Abend schafft man nämlich vermutlich maximal ein Drittel der möglichen Themen. – Und damit wälze ich nun die Qual der Wahl auf die Kollegen RGVs ab 😉
Session Description:
SQL Server is considered “secure by default”, but one of the most often successfully attacked targets is the data that resides in a Database Server. Most of the exploited weaknesses in a SQL Server environment are due to misconfiguration weak security settings or inadequate coding practices.
In this purely demo-based security session, I am showing several attack scenarios on different layers. Due to special request this includes some special SQL Injection types. Furthermore I show how an evaluation of privileges attack is possible due to a not uncommon configuration as well as an “insider-exploit” with a database root kit.
Note that in this kind of session I do not give instructions on “how to hack” but rather I am highlighting common weaknesses – “what can happen and under which circumstances”.
(Almost) no slides: just Demos Demos Demos
Contents
Web)Application Layer
- My form and the WAF don’t let anything pass through – or do they?
- Standard SQL Injection
- Blind / Error-based /Time-based SQL Injection, Encoding Injection
- 2nd Order SQL Injection
- Privilege Escalation via SQL Injection and trustworthy
- automated attacks using tools, further “features”
- “case of the unkillable transaction” – DoS Attack via SQL Injection
- SQL Server Row- and Cell-Level Security – Disclosure vulnerability
- XML Bomb
- A bit of fun with collation
- Tables without a name? Or no tables at all?
“guaranteed unique objectnames” 😉
- Tables without a name? Or no tables at all?
Inside the Network
- Reconnaissance: Detecting SQL Server Instances
- SQL authentication
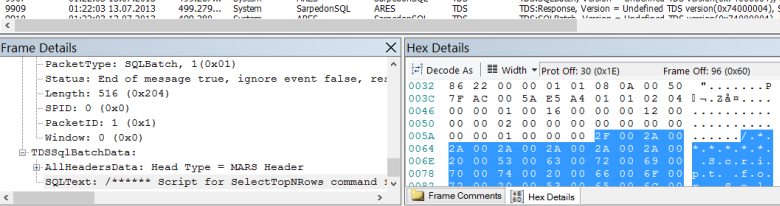
- Watching SQL Traffic (Login + Select)
- Cracking Passwords – possible? How?
- Reading passwords from memory
Server & database-Level – attacks from inside, Part 1: evil Consultant
- Was ein Consultant so hinterlassen kann
- Automated install of a SQL Server rootkit
- „When the guest switches the party“
- Circumventing denies by “guest-guest-impersonation“ – first shown at PASS Summit 2010 in Seattle 🙂
Server & database-Level – attacks from inside, Part 2: evil Developer
- „Know your rights“
-
- Transfer-Schema Attack – first shown at PASS Summit 2010 in Seattle 🙂
- „Everything belongs to me“ – does it?
-
- Database-ownership-chaining
- Db_owner underestimated & exploited
- Schema-ownership-chaining
Recent Security Reports:
- Data Breach Investigations Report
- White Hat – Website Security Statistics Report, May 2013
PASS Essential “SQL Server 2012 Database-Security, Best Practices & Pitfalls”
- 25 Sept. 2013, Düsseldorf
www.sqlpass.de/Portals/0/PassEssentials/2013-09-25_PE_AWO_Datenbank-Sicherheit_Datenblatt_web.pdf
Security Workshops, November 2013:
- Securityworkshop (SID) für SQL Server Entwickler (1 Tag) “Die Basis für ein sicheres Backend: Von Ausführungskontext bis zu Verschlüsselung.” Frankfurt am Main, 21 Nov. 2013
- Securityworkshop (SIA) für SQL Server Administratoren (1Tag) “Systemsicherheit für SQL Server: Von Authentifizierung bis zur Sicherheits-Überwachung.” Frankfurt am Main 2 Dec. 2013
enjoy and until soon – in your regional chapter, in your company, at a SQL Server Master-Class or at some conference – just say hello if you see me
Andreas